- Gain greater control over user access risks, segregation of duties, compliance, and audit by leveraging cutting-edge technology. Embedded AI, machine learning, and predictive analytics continuously identify potential risks and provide optimized suggestions to streamline access management.
- Excessive access and unnecessary ERP risk have been the byproduct of complex access management solutions, siloed visibility, and an over-reliance on manual processes. Appsian is the first platform that presents each authorization-related decision from multiple angles, including financial risks, to help automate access control management.
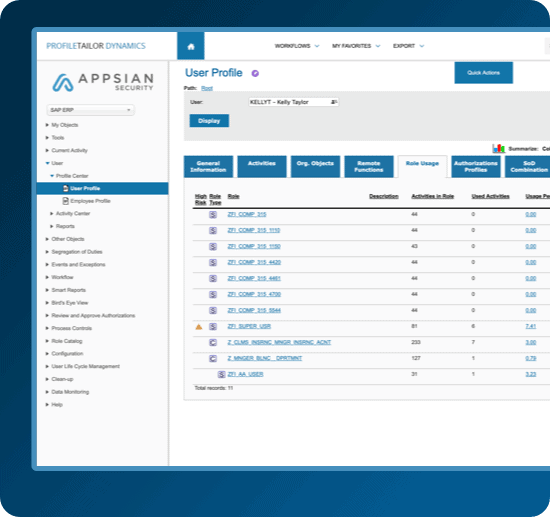
- As an advanced behavior-based monitoring and analysis solution, Appsian enables organizations to easily organize, understand, and control employee authorizations across multiple ERP systems. It delivers unprecedented visibility of real-time authorization usage, performs ongoing monitoring of each and every user, and sends alerts of any unusual or suspicious activity.