Appsian How-To: Enforce Transaction Level Policy Controls in SAP
The typical business application’s role-based access control (RBAC) security model provides poor dynamic transaction level policy control enforcement. In this video demonstration, you’ll see how to enforce transaction level controls in SAP using attribute-based access controls (ABAC). You’ll also see how Appsian Security’s analytics platform, Appsian360, allows you to monitor user behavior around those transactions and spot deviations from normal behavior.
Gartner recommends transitioning from the static RBAC security to Adaptive Security found in an Attribute-Based Access Control (ABAC) security model. ABAC allows you to set controls based on policies and enforce that control at the transactional level or at the field level. The good thing about this is we can enforce transaction level controls in one place, and we can make it work across the different transactions. In other words, it’s a one-to-many level of control.
You can then use Appsian360 to monitor the most often run transactions, where they are most frequently run from, and the active status of these transactions.
What is Adaptive Security?
Adaptive security is an approach to managing security that analyzes behaviors and events to protect against and adapt to threats before they happen. With an adaptive security architecture, an organization can continuously assess risk and control effectiveness monitoring and automatically provide proportional enforcement that can be dialed up or down to fit its need.
- Adaptive Security is configured using combinations of contextual attributes, to enforce policy requirements into the access controls, thus automating policy enforcement.
- Adaptive Security constantly monitors and analyzes detailed user behaviors at the transaction and data level to detect threats, and then adapts the security controls to respond to threat with a mitigation action.
- The specific policy requirements configured into the access controls become the “key risk indictors” that Appsian360 can monitor to detect and report anomalies and threats.
Contact us today for a full demonstration on how to implement policy controls at the transaction level in your ERP applications.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
Data Loss Prevention: 7 Best Practices for SAP Security
A constantly evolving threat landscape and compliance environment with inconsistent standards have made data loss prevention (DLP) a vital component of an organization’s SAP data security strategy. The global cost of data breaches hit a record-high in 2021 ($4.2 million per incident), highlighting the importance of a robust DLP strategy to protect organizations from financial, legal, and reputational damages.
What Is Data Loss Prevention?
Data Loss Prevention is the practice of identifying and preventing data breaches, exfiltration, or unwanted loss or destruction of sensitive data. Businesses use DLP solutions for SAP and PeopleSoft applications mainly to:
- Secure Personally Identifiable Information (PII)
- Comply with data security and privacy regulations
- Protect intellectual property critical to the organization
- Prevent unauthorized transfer of data outside the organization
Seven Data Loss Prevention Best Practices
For any DLP strategy, you need to understand which organizational data to secure, where that data resides, who has access to that data (and when), and how the data should be used. Unfortunately, data loss is difficult to spot because data routinely moves in and out of an enterprise and closely resembles normal traffic. Let’s take a look at a list of data loss prevention best practices that have helped our customers achieve their data security goals and meet compliance standards.
- Configure Dynamic Data Loss Prevention Policies
Preventing unauthorized exposure of sensitive information and protecting against insider data leakage begins by configuring contextual, attribute-based DLP policies that restrict transactions based on user and data attributes. Unfortunately, traditional role-based access controls (RBAC) can’t completely safeguard data in dynamic environments as static roles fail to leverage contextual attributes such as time of the day, geolocations, IP address, transaction type, etc.
- Establish Clearly Defined Rulesets for Segregation of Duties
Establishing a clearly defined ruleset for segregation of duties that divides business processes between multiple users helps limit the risk of fraud and error while ensuring that a user’s access privileges do not conflict or violate business policies.
- Deploy Policy-Based Data Masking and Redaction
Companies can enable dynamic data masking to reduce unnecessary exposure of sensitive information while allowing employees to do their jobs. For example, masking specific fields on a page an employee is accessing. Or using click-to-view masking to unmask data or require an MFA challenge before data is revealed to log access to a particular field. And don’t forget to protect non-production environments where dynamic data masking ensures development or testing teams can only access the data they need and nothing more.
- Continuously Monitor Data Access And Usage
Monitoring user behavior around data access and usage in real-time at a granular level provides visibility into how users interact with sensitive data, triggering security event alerts for high-risk access and abnormal activity at the field level. (Native application logging capabilities cannot tell the difference between malicious user activity and normal usage.)
- Increase The Levels Of Access Control & Monitoring for High-Privilege Users
Because privileged user accounts are magnets for hackers, companies should isolate activity and access data by these accounts to ensure integrity and alignment with current business policies. For example, an employee from the HR department needs access to payroll information to do their job, but do they need that access outside of office hours or from an unknown IP address?
- Closely Monitor Report and Query Downloads
Monitor instances of query running and download attempts, ensuring that sensitive queries are not being downloaded onto unauthorized devices, from suspicious locations, or outside business hours.
- Leverage DLP Solutions to Automate As Much As Possible
For all the features and value ERP systems provide, they lack the functionality to provide a dynamic, automated data loss prevention solution. Automating DLP processes across the organization allows you to enforce dynamic policies to identify and protect data before it exits the organization. In addition, automating compliance audits allows you to constantly monitor data access and usage and alert security teams to abnormal activities.
How Appsian Security Helps Enable Your SAP Data Loss Prevention Strategy
Whether careless or malicious, employee, partner, or contractor, it can be difficult to tell the difference between a user’s regular activity and activity intent on causing harm or theft. The Appsian Security Platform (ASP) helps SAP customers deploy these data loss prevention best practices, and many more, to prevent unauthorized exposure and exfiltration of sensitive data, PII, and intellectual property.
By configuring dynamic access controls, you can uniformly enforce policies that restrict transactions based on user and data attributes. In addition, you can deploy policy-based data masking that help you comply with data security and privacy regulations by reducing the exposure of high-risk data.
Contact us today for a demonstration and see for yourself how Appsian Security can help with your data loss prevention strategy.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
SAP Access Controls: How RBAC & ABAC Work Together
To ensure employees remain productive in a dynamic and hybrid work environment, organizations use SAP access controls to allow their workers remote and secure access to ERP data, transactions, and self-service modules. Unfortunately, the existing SAP role-based access controls (RBAC) have reached their limitations in a dynamic workplace because static roles do not leverage contextual attributes.
Understanding SAP Access Control Using RBAC
Functionally, role-based access control (RBAC) is a policy-neutral approach to granting (or restricting) SAP access based on the roles of individual users in the company. Since RBAC was intended for on-premises data access from behind a corporate firewall, it creates a very strict, static set of permissions. You either have access or you don’t.
RBAC has always provided a strong foundation for setting SAP access controls. However, the way people are interacting with data resources is constantly evolving and RBAC is struggling to keep up.
Enhancing RBAC by Using Attribute-Based Controls in SAP
Organizations are looking for more flexible and secure ways to grant users access to only the information and resources they need to perform a particular task. This dynamic approach to SAP access controls enhances RBAC by considering different “attributes,” enabling security policies to be dynamic and “data-centric” and leveraging a user’s context of access to determine access to data. By incorporating these attribute-based access controls (ABAC), organizations can control user access more precisely, and better balance policy and security requirements.
The more attributes you can incorporate, the more precisely you can define what, how, and when a user or group of users can access data. Unlike RBAC, ABAC allows you to use contextual information such as project ID, company code, IP address, location, device type, and more to authorize access.
The RBAC + ABAC Hybrid SAP Access Control Model
Appsian Security extends and enhances existing SAP access controls by combining RBAC security capabilities with attribute-based policies. Starting with RBAC, organizations set the foundation of their access policies. ABAC begins the moment users start to access data and transactions and considers the context of access (who, what, where, when, and how) before allowing a user to access transactions or data.
The key benefits of the RBAC + ABAC hybrid model from Appsian Security include:
- Reducing Attack Surface
Organizations can reduce their amount of accepted risk by applying granular business policies and contextual access controls to strengthen data-level and transaction-level security. - Dynamic Data Masking
You can dynamically enforce data masking or outright restriction policies to any field in SAP when using real-time contextual policies that balance security and usability. - Reinforcing SoD Policy Violations
Adding ABAC to RBAC allows you to apply preventive controls in segregation of duties (SoD) exception scenarios. By doing so, you can prevent SoD violations while still allowing the flexibility of conflicting roles to be assigned (when necessary) and reinforces role-based policy to mitigate over-provisioning.
Without a solution like Appsian Security, the closest organizations can come to granting policy-based access to SAP is through customization or adding role derivations to a user for each attribute. Both options are costly and add complexity and overhead to role management in the long run.
Contact us today and schedule a demo to see how Appsian can help you enforce SAP access controls beyond the standard RBAC model.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
How to Protect Your ERP With an Adaptive Security Model
Agility is the name of the game in today’s ERP data security landscape. Organizations are being challenged to detect threats as they happen, quickly address vulnerabilities, and continuously improve their security posture while protecting crucial ERP data as well as their overall business. One strategy that is helping organizations become more proactive is aligning to an adaptive security model.
Focused on operationalizing agile, context-aware, and adaptive technologies, an adaptive security model enables organizations to strengthen security and leverage automation for continuous improvement.
What is Adaptive Security?
Adaptive security is an approach to managing security that analyzes behaviors and events to protect against and adapt to threats before they happen. With an adaptive security architecture, an organization can continuously assess risk and control effectiveness monitoring and automatically provide proportional enforcement that can be dialed up or down to fit its need.
Figure 1: Adaptive Security Architecture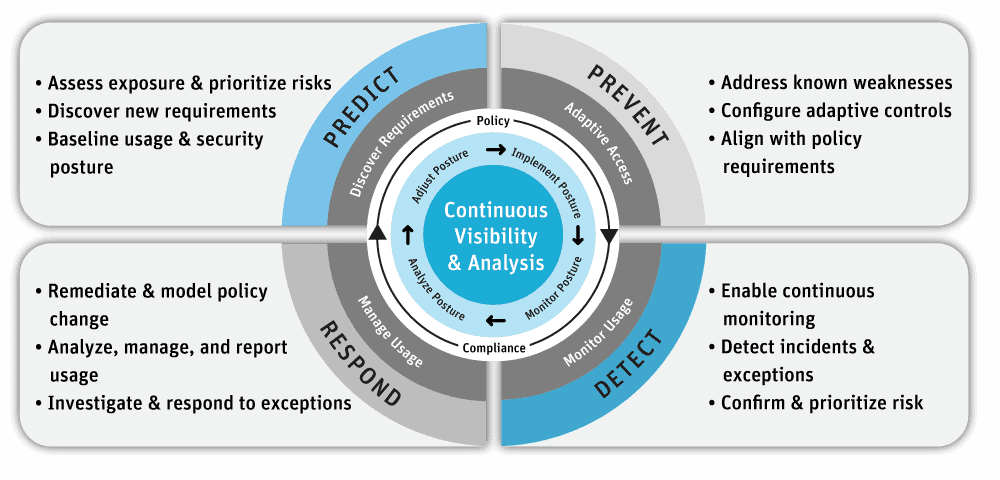
You’ll note that there are four stages of an adaptive security architecture: Prevent, Detect, Respond and Predict. These stages help organizations transform the old static, roles-based approach to ERP data security to a continuous monitoring and risk-adaptive approach. Zero trust is a core concept to adaptive security, which promotes continuous monitoring and analysis as a starting point, enables rapid detection of behavioral anomalies, and permits rapid responses to quickly stop and resolve security incidents.
Seven Imperatives for an Adaptive Security Architecture
According to Gartner, supporting digital business transformation in an environment of advanced threats requires a new approach for all facets of security. Security and risk management leaders can use these seven imperatives of an adaptive security model to embrace the opportunities and manage digital business risks. Each imperative is Gartner’s recommended capability required of your ERP security, risk & compliance solution to enable the security model.
- Replace One-Time Security Gates with Context-Aware, Adaptive, and Programmable Security Platforms
Organizations need to replace the initial one-time, yes/no risk-based decision at the main gate to their systems (typically managed by a static authentication and authorization process) with a continuous, real-time, adaptive risk and trust analysis of user anomalies with context-aware information across the platform. Context-aware security (also known as attribute-based access controls or ABAC) uses situational information, such as identity, geolocation, time of day, or type of endpoint device. - Continuously Discover, Monitor, Assess and Prioritize Risk — Proactively and Reactively
Risks events are fluid and require constant identification, analysis, prioritization, monitoring, and response after the initial login assessment. This should include a combination of proactive and reactive capabilities. For example, if a user attempts to download a large amount of sensitive data, you need the ability to detect and prevent this action if it’s considered inappropriate. Again, the use of ABAC can provide organizations with preventative controls at the business process, transaction, and master data level. - Perform Risk and Trust Assessments Early in Digital Business Initiatives
This imperative focuses on early risk assessment, meaning performing risk and trust assessments early in the process execution. - Instrument Infrastructure for Comprehensive, Full Stack Risk Visibility, Including Sensitive Data Handling
This is a continuous risk assessment recommendation across the full tech stack and data handling to enable adaptive security decisions. - Use Analytics, AI, Automation and Orchestration to Speed the Time to Detect and Respond, and to Scale Limited Resources
This imperative recommends using artificial intelligence, machine learning, analytics, and automation to increase the efficiency and effectiveness of risk detection, analysis, and response capabilities. - Architect Security as an Integrated, Adaptive Programmable System, Not in Silos
Avoid silos! Organizations shouldn’t perform risk assessments in individual isolated silos. Instead, aggregate continuous risk assessments provide a more accurate view of the organizations’ risk exposure. - Put Continuous Data-Driven Risk Decision Making and Risk Ownership into Business Units and Product Owners
This imperative encourages better transparency and decision-making through better data-driven risk visibility to the business unit leaders for their own decision-making.
How Appsian Security Helps Organizations Achieve Adaptive Security
The problem we help companies overcome: In its current form, the static data protection approach utilized by most organizations lacks the effectiveness required to manage today’s complex challenges. Without an accurate picture of risk exposure in their organization, security administrators protect data the only way they can – with restrictive measures under the principle of least privilege and zero trust.
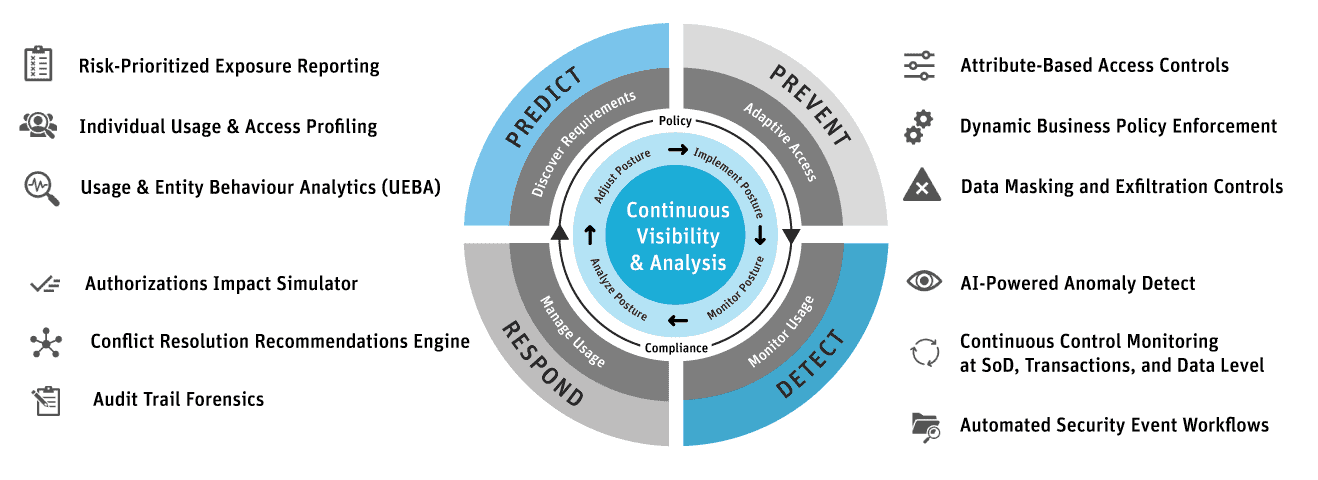
Here’s how Appsian Security’s capabilities align to the Gartner adaptive security model. The Gartner adaptive security model is illustrated with the Appsian Security solution capabilities aligned with their Predictive & Discovery Requirements, Preventative & Adaptive Access, Detective & Monitor Usage, and Respond & Manage User capabilities.
Five Ways Appsian Security Helps Improve ERP Data Security
Organizations are being challenged to protect access to sensitive and confidential data while improving their ability to analyze security data and detect attacks in progress. Here are five ways that Appsian Security can help your organization meet these challenges:
- The capabilities of the Appsian Security solution align with Gartner’s Seven Adaptive Security Imperatives.
- Appsian offers context-based access controls that can prevent, detect, and respond to user anomalies at the business process, transaction, and data level.
- Appsian enables continuous monitoring and real-time reporting of user anomalies.
- Appsian offers artificial intelligence, machine learning, and automation to increase the efficiency and effectiveness of your risk detection, analysis, and response capabilities.
- Appsian can automate the enforcement of your policy requirements at the business process, transaction, and data level.
Contact Appsian today to learn how our zero trust solutions can anchor your adaptive security architecture and improve your ERP data security.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
How Appsian Reduces Risk in SAP Procurement Transactions
The sheer breadth and complexity of the procurement process can make maintaining effective internal controls difficult. Organizations must implement business process controls to ensure that employees only have access to SAP procurement transactions appropriate to their role and that the activity within these transactions falls in line with their established business policies. Having tightly aligned controls that prevent policy violations in the first place is critical to reducing the level of accepted risk in procurement business processes.
And this brings us to a key challenge in SAP procurement processes. Relying solely on SAP’s static role-based access controls (RBAC) has its limitations. Without the ability to consider factors beyond a user’s role and privileges, preventive controls may be impractical in certain scenarios, forcing reliance on detection and remediation in hindsight.
Enforce SAP Procurement Transaction Policies with Dynamic Access Controls
With the dynamic nature of procurement processes, extending your business process controls strategy to include data-centric and context-aware functionality can significantly reduce your risk exposure. Organizations using SAP ECC and SAP S/4HANA can strengthen policy enforcement by leveraging dynamic, attribute-based access controls (ABAC). Appsian extends SAP’s existing security model by enabling a fine-grain approach that shrinks the gap between business goals and security controls.
Let’s look at some specific use cases across SAP procurement transactions to demonstrate how Appsian can reduce SAP business process risks in today’s dynamic access environment.
Dynamically Controlling Purchase Order Creation
Purchase order creation is an important procurement transaction that should be controlled by an assigned threshold level and approval limits. Appsian allows you to easily manage risks associated with the purchase order process by extending dynamic controls into SAP based on factors such as PO dollar amount, location, time of day, and more.
For example, let’s look at a couple of employees:
| Employee | Total PO Threshold | Create POs when Remote? |
| George | Up to $5,000 | No |
| Gracie | Up to $25,000 | Yes. Between 8 am-5 pm |
You can allow George only to create POs that do not exceed $5,000 in value. He is also blocked from creating POs outside of the corporate network. For Gracie, she has the company’s approval to create POs up to $25,000 and can do it when working remotely as long as it is during normal business hours of 8:00 am to 5:00 pm.
Dynamically Enforce Segregation of Duties
During the procurement business process, there is a need to control the PO’s life cycle using Segregation of Duties (SoD). That means the same person can’t perform PO creation and GR (Goods Receipt) posting followed by IR (Invoice Receipt) posting.
Segregation of Duties policies that rely on static role-based rules can create unwanted business risk because they lack visibility into attributes that define actual conflicts of interest. This gap also carries over into SoD audit logs, resulting in excessive false positives when SoD exceptions have been made.
Appsian allows you to stop unauthorized user activity in real-time using a data-centric approach to enforce SoD controls. Our preventive SoD controls correlate user, data, and transaction attributes, along with identified SoD conflicts, to block conflicting transactions at runtime – even if they have the role-based privileges to perform the transaction.
This approach can add flexibility to procurement processes by allowing users with SoD exceptions to perform conflicting transactions that do not pose actual SoD violations while preventing those that do. The preventive SoD controls can also act as a safeguard to stop any SoD violations that may originate from privilege creep, such as a user changing roles without prompt deprovisioning of old privileges.
Limit Access to Sensitive Data by Masking with Conditions
Because the SAP procurement process touches different departments, it’s important to ensure that users do not have access to data or transactions outside of their roles and responsibilities. From protected PII to privileged financial information – this data carries risks that organizations must address.
Alas, there are no masking capabilities available out of the box in SAP. As a result, privileged users can access sensitive data fields even when access is unnecessary. This kind of unchecked data exposure leaves a massive threat surface that is vulnerable to exploitation and leakage.
Appsian’s Dynamic Data Masking provides SAP customers with fine-grained control over which sensitive data fields they can mask for specified users in the context of any situation. For example, you can decide to mask PII, account names, account numbers, etc., if access comes from an unmanaged device, unknown IP range, or outside typical working hours. Likewise, you can easily mask sensitive data in transactions where exposure is unnecessary for a certain role to do the task at hand.
Appsian: The Dynamic Approach to Reducing SAP Procurement Risks
Managing SAP procurement transactions exist in the overall category of reducing SAP business process risks. It’s a persistent challenge facing organizations of all sizes.
Contact the experts at Appsian today to learn how we can help you face this challenge head-on with our dynamic approach to managing your SAP business process controls.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
How Does Appsian Work with SAP GRC Access Control?
At the SAPinsider 2020 virtual conference experience, one of our product demo attendees asked how Appsian works with SAP GRC Access Control. We get this question a lot as SAP security and system professionals explore adding attribute-based access controls (ABAC) to the native SAP role-based access controls (RBAC) to streamline and strengthen access policy management and enforcement. Sometimes there is confusion about whether ABAC is enhancing or replacing their RBAC. Let’s take a quick look at how Appsian’s ABAC works with and enhances SAP GRC Access Control.
What is SAP GRC Access Control
Organizations use SAP Governance, Risk, and Compliance (SAP GRC) to manage regulations and compliance and remove any risk in managing critical operations. One of the SAP GRC modules that helps organizations meet data security and authorization standards is SAP GRC Access Control. This module ensures that the right access is given to the right people with RBAC. It uses templates and workflow-driven access requests and approvals to streamline the process of managing and validating user access and provisioning. Without SAP GRC, for comparison, a person is creating all the roles from scratch and assigning privileges to them.
Appsian Enhances SAP GRC with Attribute-Based Access Controls
Appsian combines the SAP GRC role-based access controls with an attribute-based access control solution that delivers an ABAC + RBAC hybrid approach. This enhanced approach enables granular control and visibility that delivers a wide range of business benefits and lets you deploy data-centric security policies that leverage the context of access to reduce risk.
Appsian overcomes the limitations of traditional RBAC, allowing you to fully align SAP security policies with the objectives of your business and streamline audits and compliance.
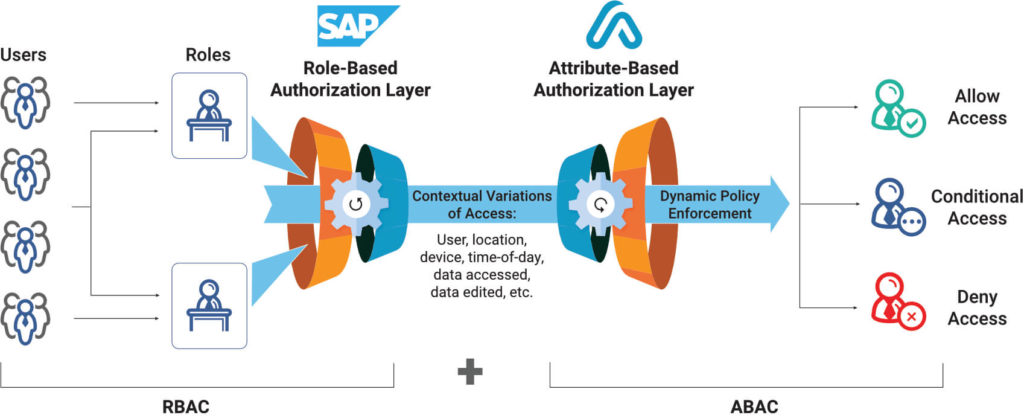
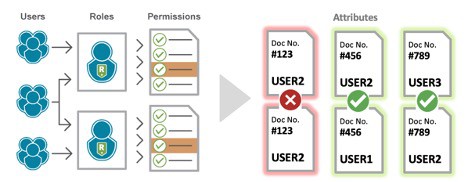
As you can see in this illustration, ABAC begins the moment users start to access data and transactions. Where RBAC assigns access based specific roles, ABAC considers the context of access (who, what, where, when, and how) before allowing access to transactions or data. Customers can set up additional rules that allow conditional access, for example, masking specific data fields or limiting the number of transactions after a particular time of day) or entirely denying access based on factors such as an unknown IP address.
Real-Time Analytics for SAP Security & Risk Management
With Appsian360, our real-time analytics and reporting tool, Appsian can enhance the SAP GRC reporting capabilities with direct, real-time visibility into transaction usage, violations, and compliance risk. Additionally, customers can:
- Monitor transaction usage, master data changes, and SoD violations
- View actual SoD violations with user, data, and transaction correlation
- Segment reports by user/data attributes
- Drill down into end-user usage events
Appsian360 provides analytical reports to drill down into end-user usage events to capture business risks and anomalies, and usage events that tie back to compliance risks.
The ABAC + RBAC Hybrid Approach to SAP GRC Access Control
By combining data-centric security capabilities with attribute-based policies, Appsian extends and enhances the existing SAP GRC internal access controls and improves the reporting and auditing capabilities.
Contact us today and schedule a demo to see how Appsian can help you enforce access controls beyond the standard RBAC model of SAP.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
Improve SAP Access Policy Management During These Turbulent Times – and Beyond
In these less than ordinary times, organizations are dealing with disruption at a frequency higher than ever before. An unfortunate side-effect of this COVID crisis has been its impact on employees. Whether furloughed, laid off, or set to take on broader responsibilities, change is happening. And naturally, these changes must be reflected in your ERP applications’ access policy management.
The uptick in user provisioning is placing additional pressure on SAP security and IAM teams, already burdened with securing remote access to applications for people working from home. These days, you have to wonder if IT professionals are feeling like they’re chasing something they can’t keep up with. And that leads to problems.
Joiners, Movers, and Leavers
The user provisioning process typically encompasses three phases: joiners, movers, and leavers. In short, they are three separate scenarios – when employees are onboarded, when they switch positions/departments internally, and when employees leave the organization. Given COVID, leaving the organization could mean either termination or furlough.
If overburdened IT and security teams cannot address provisioning promptly, organizations are leaving themselves open to an onslaught of risk in times where cyber-attacks are peaking and employees are already feeling stressed out.
Thanks to an enlarged threat surface from remote access, a compromised account can cause considerable damage before it is detected. Excessive privileges only multiply this risk. Alternatively, strained and disgruntled employees with excessive privileges may be tempted by fraud, especially in cases where segregation of duties (SoD) should be in play. If an employee was given extra responsibilities that necessitated new roles, potential conflicts might be overlooked.
Three Tips for Improving SAP Access Policy Management
Setting the roles is only one step. You don’t want to give everybody the same kind of visibility or access to data, depending on their role. This is a great time to invest in data security technology and establish more granular access policies. Here are three tips for improving your SAP access policy management:
1: Leverage Attribute-Based Access Controls (ABAC) to Simplify User Provisioning
Organizations with similar roles spanning multiple business units turn to role derivatives to ensure access is segmented appropriately. While effective from a control perspective, managing these roles can prove burdensome as the number of role derivatives multiply with each branch-off.
For example, a manufacturing organization has 50 functional roles shared by users across 10 different plants. Using role derivatives, they would end up managing 500 different roles to ensure access is segregated appropriately. The sheer scale can be overwhelming to your SAP security team to begin with – and now we’re adding in all the joiners, movers, and leavers from COVID-induced workforce changes.
The purpose of roles is to be scalable! We want access policies that are one-to-many, not one-to-one. To gain back simplicity and lighten the load on your IAM teams, organizations can extend their existing role-based access control (RBAC) model with attribute-based access controls (ABAC). ABAC allows you to easily bring fine-grained “attributes” into your authorization decisions. In the example above, one could go from managing 500 role derivatives down to 50 roles and 1 supplemental ABAC policy that can consider the differing factor, a user’s assigned plant code, to automatically segregate their access appropriately.
2: Reduce Your Attack Surface with Fine-Grained Entitlements
The Principle of Least Privilege is a crucial tenet in information security. The goal is to minimize risk by providing users with the minimum level of access needed to perform a task at hand. This is the purpose of existing role-based access controls – e.g., an HR manager should not have access to finance transactions because it is out of their scope. However, this does nothing to protect data within their scope. Should the HR manager have access to social security numbers or compensation data at all times? After hours? Remote? The answer is likely, no.
Organizations can reduce their amount of accepted risk by applying granular business policies and access controls to strengthen data-level and transaction-level security. Leveraging ABAC, you can enforce risk-aware controls to place limitations on what users can access within your application, from where, when, how they can access, and what they can do with data. ABAC provides an additional level of security by incorporating additional context like geolocation, time of day, and IP address. This ensures appropriate user access and prevents users from having more access than they need. Want sensitive data masked when access is outside your network? Done. Want to block high-risk transactions after hours? Easy.
3: Manage the Identity Lifecycle with User Activity Monitoring
Organizations should always engage in some kind of user activity monitoring, regardless of the number of joiners, movers, and leavers they’re dealing with. But this monitoring must extend beyond time-consuming and potentially expensive manual audits. You want to make sure the access control policies you’ve established are working and that you’re watching for anomalies. Some user activity to consider monitoring includes:
- Identifying high-privilege user activity and critical transactions while closely monitoring and auditing on a regular basis
- Continuously monitoring access across peer group activity for visibility into who changed what in regard to roles and permissions
- Setting risk-aware alerts such as location of user, device accessing network, etc. This monitoring is vital for streamlining threat detection and alleviating the manual process typically required for threat response
Assign Ownership and Responsibility Over User Provisioning
While you’re monitoring user activity, don’t forget to put some eyes on your IT and security teams. You’ll want to assign ownership and responsibility to whoever responds to access requests and reviews temporary team member access. Keep good records as to why approvals are made or changed. You’ll want to approach this in a way that is easily audited. (Tip: email is not that process).
Conclusion
There are many moving parts and people that IT staff and security teams must manage. Leveraging tools that can improve an organization’s SAP access policy management will go a long way towards protecting important data and easing the burden on stressed IT and security teams.
Schedule a demonstration today and learn how Appsian can mitigate SAP business risks with ABAC and User Activity Monitoring.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
Your Network Access Could Be for Sale on the Dark Web. Why ABAC is Critical for ERP Data when Your Network is Vulnerable
Thanks to TV commercials for identity protection services, you’re forgiven for thinking that that dark web is primarily a place where criminals and hackers buy and sell personal information such as credit cards, usernames and passwords, and social security numbers (and other PII). Lately, however, the dark web has seen a flurry of activity for offers to purchase corporate network access, according to a recent “Access for Sale” report from Positive Technologies.
Criminals Are Becoming More Interested in Corporate Network Access
Just a year ago, according to the report, cybercriminals were focused more on trading in access to the servers of private individuals for as little as $20. During the second half of 2019, Interest has since picked up in the sale of access to corporate networks. In Q1 2020, the number of postings advertising access to these networks increased by 69 percent from the previous quarter. Prices have also increased: the average cost of privileged access to a single local network is now in the $5,000 range. Additionally, hackers are offering a commission of up to 30 percent of the potential profit from a hack of a company’s infrastructure.
It’s bad enough that your threat surface has increased due to so many employees working from home, now you have a posse of hackers roaming the dark web looking for bounties to collect. We have a few suggestions to help you keep your ERP data safe even if hackers manage to gain access to your corporate network.
Adopt Attribute-Based Access Controls (ABAC) to Strengthen ERP Data Security
Companies using ERP systems are already leveraging role-based access controls. These controls, which align data access privileges and job function resources, provide a baseline for data governance. With the rapid expansion to a remote workforce earlier this year, organizations needed to create more detailed and more dynamic access controls—policies to determine who, what, where, when, and how workers can access ERP data and what transactions they’re allowed to perform.
With attribute-based access controls (ABAC), a company can incorporate additional context such as geolocation, time of day, and IP address to both ensure the appropriate user is accessing the resources and prevent users from having more access than they need. For example, if the organization knows that an employee should be working from Connecticut, ABAC can prevent access to resources, mask highly sensitive data, or prevent a transaction entirely if the user’s location is suddenly California – or a foreign country.
These granular, data-centric access privileges can help an organization ensure that users–internal or malicious–do not get too much access to important ERP data – limiting the potential negative effects of a network intrusion by hackers.
ABAC Should be Coupled with User Activity Monitoring
Let’s revisit how ABAC helps organizations establish roles and permissions to determine who, what, where, when, and how workers can access ERP data and what transactions they’re allowed to perform. It’s important that you don’t set these controls and “forget” them. You want to make sure what you’ve established is working and to watch for any anomalies that reveal unusual or unwelcome activity.
Most organizations are already performing some kind of monitoring of user access – but it has to extend beyond manual audits of instances of logging in and logging out of applications and what pages were displayed. Understanding data access, usage, and transactions performed is now a key requirement when maintaining visibility over business data and enforcing security policies.
Here are five details we recommend monitoring (more details here):
- Who – Details of the User Accessing the Data
- What – Details of the Data Being Accessed
- Where – Location Where the User is Accessing the Data
- When –Time of Day When User is Accessing Data
- How – Type of Device Accessing Data
Data is only as useful as the insights it provides. Using an analytics platform that includes granular access details, rapid aggregation, and visualization of user access data is a crucial requirement for data security.
Conclusion
You know that hackers are already looking for any and all security lapses on your perimeter to gain access to your corporate network. The “Access for Sale” report serves as an important reminder that hackers are willing to do anything to gain an advantage, and organizations must deploy a variety of ERP data security protocols in addition to the standard role-based access controls.
Appsian has helped hundreds of organizations that leverage legacy ERP applications like PeopleSoft and SAP ECC strengthen their data security posture with ABAC and user-activity monitoring.
Request a demonstration of the Appsian Security Platform today. Learn how Appsian can help you manage the risks of the dark web in little as 30 days!
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives
How to Streamline the SAP Segregation of Duties Exception Process Using Attribute-Based Access Controls
Secure, compliant, and efficient business processes are critical to enterprise operations. In SAP, Segregation of Duties (SoD) is a key principle in making this possible.
What happens when an SoD exception is necessary?
Often times a user will need to be granted roles and privileges that pose a conflict of interest. It could be that an employee is part of a small department, or that a security clearance precludes others from involvement. Whatever the reason, this user needs the ability to handle multiple steps in a business process – and an exception is made.
Here’s where things can get tricky. Once an SoD exception is made, your standard preventive controls are no longer effective. This is one of the major shortfalls of SAP’s static, role-based access controls.
Shifting from a preventive approach to a detective approach…
… you must now gather access logs, filter out false-positives, and finally, send to the appropriate control owner to review and sign-off. Besides the additional overhead of manual reviews and approvals, detective controls create room for human error and increase the dwell time before red flags are caught.
So why are current SAP SoD Controls limited?
Without the logic ability to decipher potential violations from actual violations, preventive controls are a non-starter. Your (preventive) SAP access controls determine authorizations based on two things: 1.) a user’s role and 2.) the role’s associated permissions (think transactions.) While this works in the vast majority of cases, enforcing SoD requires controls with more granularity.
Let’s take a look at what an actual SoD violation entails
The whole objective of SoD is to avoid conflicts of interest in your business processes. Although, conflicting transactions do not necessarily pose a conflict of interest, unless the subject is the same.
For example, a user performs the transactions to create and approve multiple purchase orders. Looking at the transactions themselves, this activity has the potential for violations. Looking deeper into the PO details, you may see that the user never created and approved the same PO – therefore no violation was made.
SAP can show you 1.) the user and role, and 2.) the transactions performed, but is missing the 3rd component: the field-level values in the PO itself. This lack of visibility into attributes beyond roles and permissions is what makes preventive controls a non-starter and clutters SoD audit logs with false-positives when exceptions have been made.
The Solution? Enforcing SoD Policy with Attribute-Based Access Controls
Attribute-Based Access Controls (ABAC) enable the use of “attributes” in authorization decisions. These attributes can be anything from user details such as role, department, nationality, or even a user’s security clearance level. Additionally, access context such as IP address, location, time, device and transaction history can be considered. And most importantly for SoD, data attributes can now be used in authorization logic. This means that field-level values within SAP can be used to determine whether to block or allow a transaction, and these details can further be used in reporting activities.
In the Purchase Order example above, data attributes can be used to identify whether a user performed the first transaction and make the correlation that performing the second transaction would result in a violation.
Combining SAP’s role-based access controls (RBAC) with an attribute-based access control (ABAC) solution enables granular control and visibility that delivers a wide range of business benefits.
Newfound Flexibility in SoD Exception Scenarios – RBAC + ABAC Hybrid Approach
The RBAC + ABAC hybrid approach opens the possibility to apply preventive controls in SoD exception scenarios. By doing so, you can offer users the flexibility an exception provides while still preventing any actual violations from happening.
Together, this hybrid approach (RBAC + ABAC) enables a dynamic SoD model that prevents violations while still allowing the flexibility of conflicting roles to be assigned (when necessary) and reinforces role-based policy to mitigate over-provisioning.
RBAC + ABAC Hybrid Approach Using Appsian
Appsian adds an additional authorization layer to SAP GRC Access Control that correlates user, data and transaction attributes, along with identified SoD conflicts, to block conflicting transactions at runtime.
Contact Us to learn more about how a hybrid access control approach can strengthen Segregation of Duties (SoD) at your organization.
Put the Appsian Security Platform to the Test
Schedule Your Demonstration and see how the Appsian Security Platform can be tailored to your organization’s unique objectives