If 2020 was the year of hastily enabling secure remote access to ERP applications, then 2021 will be the year when organizations realize that remote ERP access is here to stay – and long-term data privacy, security, and access governance strategies will be mission–critical. Securing ERP data has always been important in principle, but the mass migration to requiring remote access (in perpetuity) has kicked off a heightened emphasis on the topic.
Amongst a sea of learnings from the pandemic is that 2020 was the “coming of age” for ERP data privacy and the challenges it created. Many organizations were forced to learn the hard way that sensitive ERP data (business data and PII) are top targets for malicious activity and some of the most difficult assets for organizations to secure. Especially data in legacy business applications.
Let’s look back at the Year of the Pandemic and examine some of the data privacy events and trends we observed that will serve as guideposts for making ERP data privacy a mission-critical priority in 2021.
Variations in Access Presents Greater Data Privacy Challenges
It’s clear that working remotely is here to stay. A Gartner HR survey reveals that 41% of employees are likely to work remotely at least some of the time post-pandemic. Tech giants like Facebook, Salesforce, Twitter, and more, announced that they would continue to offer remote work and possibly move to entirely remote models permanently.
A key challenge uncovered when the pandemic forced a rapid transition to remote workforces was most organizations had data privacy and governance policies that didn’t account for variations in user access. Especially those using legacy ERP applications like SAP (ECC & S/4HANA), PeopleSoft, and Oracle EBS. After all, these applications were originally designed so users could get easy access to data inside the firewall. They were never designed for a dynamic access environment.
The fact of the matter is the roles and privileges that governed access to these systems depended on managed devices, corporate firewalls, and in many cases – 9:00 to 5:00 access demands. Remove those variables and enable access from anywhere, on any device, and at any time – and those strict privacy and governance policies were replaced by “wild west” levels of access risk.
Instead of needing to be in a specific physical location, users can access an organization’s sensitive data from anywhere. The physical and network controls that protected IT infrastructures and data privacy no longer provide the same level of confidence. Changing how companies do work requires them to change how they secure data and re-evaluate their data privacy and access governance strategies.
When it Comes to ERP Data Privacy – Identity is the New Perimeter
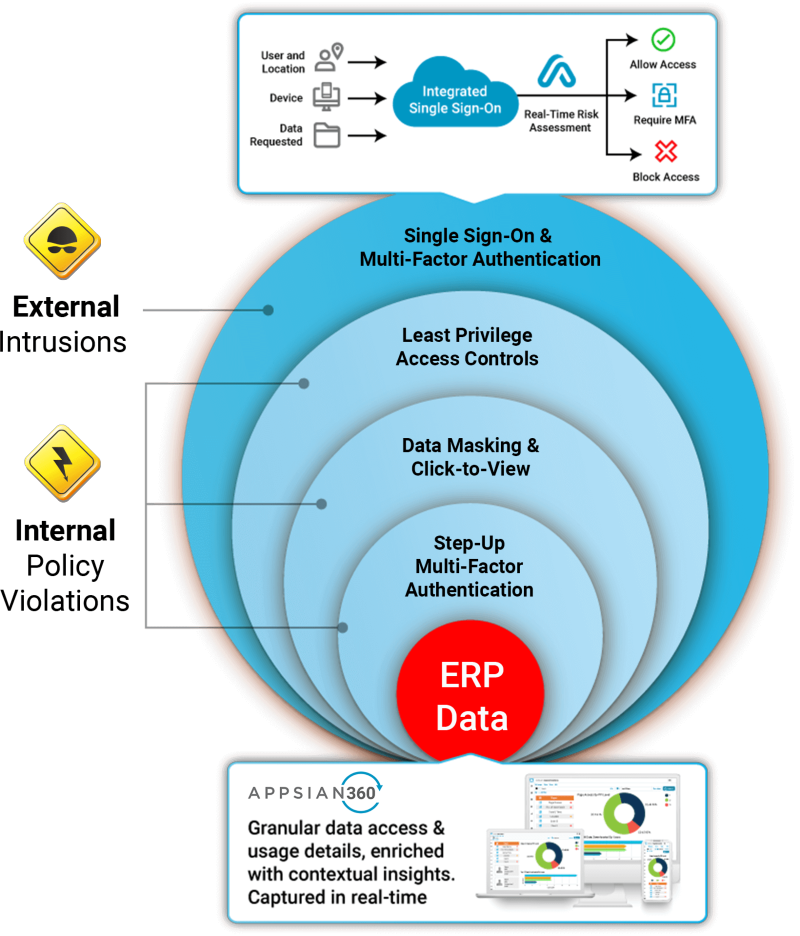
With organizations continuing to support remote access to ERP applications, they need to design policies and practices that define how data is accessed, viewed, and used – as well as the technology they’ll need to implement and enforce those policies.
A key investment is implementing dynamic capabilities to already established identity and access management (IAM) solutions. In other words, providing the ability to minimize risk by dynamically providing access based on the context of a user’s access.
Applying dynamic IAM and access governance supports traditional role-based controls but accounts for the variations in a user’s access that may indicate risk.
Further examples would be:
- Integrating an MFA on a sensitive transaction or data field and requiring a user to re-authenticate
- Deploying MFA if a user is accessing from an unmanaged device. Also known as zero-trust authentication
- Reducing levels of access privilege for super users if their access is coming from an unknown IP range. Also known as applying the principle of least privilege
- Applying dynamic data masking that masks all PII, account numbers, etc., if access is coming from an unmanaged device, unknown IP range, or outside typical working hours.
The sooner organizations realize that their perimeter is only as strong as their ability to manage user access – the better off they’ll be!
Data Privacy Regulations Mixed with Remote Access Will Only Make Compliance More Challenging
Today’s ever–changing data privacy landscape is a reminder that organizations should always be diligent about what kinds of data they are collecting, how it’s being stored, and most importantly – have the visibility to understand exactly how that data is being accessed. For example, is access suddenly coming from a hostile foreign country, or are certain data records/reports being accessed at a higher-than-normal frequency? Ask yourself, just because someone can access sensitive data, does it mean they should?
Successful organizations will invest in technologies that monitor user behavior around data access and usage, capturing contextual details like what data was accessed, where it was accessed from, user IDs, IP addresses, pages accessed, actions performed, and more – information that is paramount for compliance reporting and effectively responding to audit findings.
Hodgepodge of State-Level Data Privacy Regulations Sow Confusion
Up to now, the standard-bearer for data privacy regulations in the United States was California’s CCPA. In 2021, the number of state-level data privacy regulations is likely to increase, which is bound to further complicate matters by creating multiple compliance requirements.
Virginia is poised to become the second state to enact a data privacy bill, while lawmakers in Washington state, New York, Oklahoma, and Utah are currently weighing proposals. Meanwhile, Californians voted to approve the California Privacy Rights Act (CPRA), a series of changes made to the existing California Consumer Privacy Act (CCPA).
This hodgepodge of domestic data privacy regulations should motivate organizations to get data privacy, security, and access governance strategies in place, ensure documentation, and prepare for both financial penalties and civil actions. If 2020 was any indication (GDPR fines rose by nearly 40%), companies are likely to see more frequent and more significant fines for non-compliance in 2021.
Having Weak ERP Data Privacy Policies Will Become Expensive
COVID raised the awareness of ERP data privacy as companies struggled last year to continue with normal business operations in a remote environment. These struggles forced many leaders to establish privacy and compliance frameworks and implement the technology to support them. However, this is just the beginning.
With 2020 being a record year for data breaches – along with an ever-growing list of data privacy regulations that carry monetary fines for non-compliance – the writing is on the wall. Organizations will not be able to call themselves victims if their decades of accumulated PII and business data get exploited or breached. The monetary consequences that come from these incidences can have catastrophic effects—both against your bottom line and reputation.
Contact Appsian to learn how we can help you align your legacy ERP applications with today’s data privacy and compliance demands. Effectively scale your efforts for future mandates.